OpenID: Phishing
By David Rosen
Here at last, is the final installment in our 3 part discussion of OpenID. In Part 1 we answered the question, “What is OpenID?” In Part 2 we looked at the benefits and risks that come with using OpenID. Today in Part 3, we’re going to finish our discussion of OpenID by taking a closer look at one of it’s greatest vulnerabilities. Phishing.
Before we delve into how Phishing applies to OpenID, let’s first take a look at a traditional Phishing example:
You check your email and find a (phony) email saying, “Your credit card will be closed unless you log in now to verify our records!!!! Click here to log in and verify your account now!” The phony email very helpfully presents a hyperlink to take you (supposedly) to your Credit Card Company’s website. In actuality, the link takes you a phony site which LOOKS just like your normal Credit Card login page but with one minor difference: the URL bar has the wrong address. If you fail to notice this one difference, then upon entering your username and password, the phisher will now have full access to your Credit Card account.
There are a few key hurdles the phisher has to overcome in order for this attack to be successful:
- The email has to be convincing enough to get your attention, but not so over-the-top as to appear phony.
- You have to actually click the link provided in the email.
- The phishers have to guess which Credit Card Company login page to mimic (American Express looks different than Visa, etc).
- The URL must be good enough to fool you. It must either be similar to the real thing, hidden, or obscured.
If, at any one of these steps, you get suspicious enough to not enter your username and password, then the phisher loses.
OpenID makes this process far easier, for the phisher, by completely eliminating the first 3 of these obstacles. How can this be? Take a look at the following OpenID phishing example:
While researching woodworking, you find a nice set of plans for a workbench at www.EvilWoodWorkers.com. The plans are free to download once you create a login for the site. Luckily, they accept OpenID logins, so you won’t have to waste a bunch of time filling stuff in. You click login and then follow the instructions to enter your OpenID URL. Unbeknown to you, instead of redirecting you to your OpenID login page, EvilWoodWorkers.com simply follows the URL, and copies your login page, on the fly, to their own phishing server, which happens to have a long, unpronounceable URL. This server logs everything you type to a handy, searchable Database (based on EvilSQL 2.0). You, however, simply find yourself staring at an exact replica of your normal login page that you’ve seen a thousand times, aside from the URL. And instead of looking at that long and unpronounceable URL, your eyes gravitate to the slowly blinking cursor which is waiting patiently for you type in your username and password. The muscle memory in your fingers takes care of typing out the login details. You hit enter. You download your Work Bench Plans for free. A week later, you log back in and leave a comment thanking EvilWoodWorkers.com for the nicely done PDF.
Alas, the fly in the sauce here, is that the Phisher’s Database now contains your OpenID URL, your OpenID Username, and your OpenID password. They have obtained, with elegance and style, the keys to your castle.
Everything that you use OpenID for now belongs to the Phisher.
 How can this be? Why? The key point of failure in the above OpenID example is the redirection process. Normally (without OpenID), when you log in to a website, say Visa.com, you enter your username and password on a page hosted somewhere on that company’s domain. If you went to log in to Visa.com, and it redirected to you to some other website, with a totally different design, a different URL, and a different name, then you would be pretty darn suspicious that something phishy was going on. However, with OpenID, being redirected like that is simply business as usual. OpenID trusts the 3rd party site (Visa.com in this case) to redirect you to your OpenID provider’s log in page. That trust is the key flaw which upon which phishers will prey. The fact that you have to trust a criminal with part of the log in process is what causes this to be such a catastrophic vulnerability in OpenID.
How can this be? Why? The key point of failure in the above OpenID example is the redirection process. Normally (without OpenID), when you log in to a website, say Visa.com, you enter your username and password on a page hosted somewhere on that company’s domain. If you went to log in to Visa.com, and it redirected to you to some other website, with a totally different design, a different URL, and a different name, then you would be pretty darn suspicious that something phishy was going on. However, with OpenID, being redirected like that is simply business as usual. OpenID trusts the 3rd party site (Visa.com in this case) to redirect you to your OpenID provider’s log in page. That trust is the key flaw which upon which phishers will prey. The fact that you have to trust a criminal with part of the log in process is what causes this to be such a catastrophic vulnerability in OpenID.
Obviously, not every site is run by thieves. The real downside here is how do you know which is which? Since OpenID uses the same log in info everywhere, if the 99th site you log in to hits you with a successful phishing attack, then every previous (and future) site is now compromised as well.
OpenID is not without benefits, though. As we discussed previously, OpenID can potentially streamline and simplify the log in and sign up processes at supported websites. The potential conveniences it offers are definitely attractive.
Would I use OpenID? Sure. Given a couple caveats:
- I only intended to use OpenID at low value sites
- I only use https OpenID URL’s in order to minimize the risk of phishing
- I only use OpenID at sites with which I already have a trust relationship
OpenID stands to improve considerably as it progresses. Perhaps the best part about OpenID is that it’s Open Source. It’s development is shaped and directed by the community which uses it.
The bottom line:
If you’re an early adopter who like to play with new toys and you have a good eye for security issues (or a extremely high risk tolerance), then OpenID is a great playground.
If you are just looking to make your online life easier and more streamlined, then stay away from OpenID for now. It’s not ready for prime time yet, and even though it seems like we’ve talked about some nasty looking flaws, there are likely even more problems yet to be uncovered.

 Last week we defined
Last week we defined  I did it. I finally bit the bullet and bought an
I did it. I finally bit the bullet and bought an 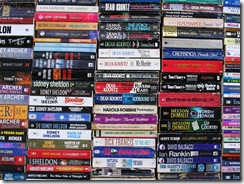 Moving toward a digital library is becoming easier as time goes by, as every day more and more books are being released in the
Moving toward a digital library is becoming easier as time goes by, as every day more and more books are being released in the  If you have signed up for a new service recently, you may have noticed an option to use something called
If you have signed up for a new service recently, you may have noticed an option to use something called  First a quick digression: What is authentication? Normally, to login to your account at a website, you first identify yourself with a username, and then you prove that you own it by providing a password. This process is “Authentication.” It doesn’t have anything to with your Plaxo contacts, your Blogger profile, or your Flickr pictures. Authentication is claiming that an identity is yours (username) and proving it (password).
First a quick digression: What is authentication? Normally, to login to your account at a website, you first identify yourself with a username, and then you prove that you own it by providing a password. This process is “Authentication.” It doesn’t have anything to with your Plaxo contacts, your Blogger profile, or your Flickr pictures. Authentication is claiming that an identity is yours (username) and proving it (password).